
Before I get started with this post, if you’re just looking for information on how people can see your protected tweets, you’ll find the answer in How Snoopers Access The Tweets in Your Protected Twitter Account If you already know that, here’s another thought-provoking observation I made about Twitter’s privacy arrangements…
Have you ever wondered what a Twitter user might be doing on the quiet, when your back is turned? Have you ever considered that there might be ways to find out, without breaking the law, and without even breaking Twitter’s Terms of Service? Well, if so, you might want to take a look at this groundbreaking article. Equally, if you care about your OWN privacy, and you want to know how vulnerable you are to covert monitoring by ORDINARY MEMBERS OF THE PUBLIC, this is going to be essential reading. Everyone should know how atrocious Twitter’s privacy measures are…
WHAT IS ‘SOFT-HACKING’?
In my Protected Twitter – I Read You Loud and Clear article I exposed the privacy flaws in protected Twitter accounts, and this article draws on similar cracks in the platform’s privacy. In this instance, I’m using the term ‘soft-hack’ to describe a way of gathering information about an individual’s Twitter use, which should, technically, be private. Or at least, that the user believes is private.
WHAT INFORMATION DOES THIS ‘SOFT-HACKING’ REVEAL?
It reveals details of significant accounts a given individual has followed, but is perhaps not following anymore, and may not want you to know about.
HOW COULD IT BE USED?
The technique could be used by someone who doesn’t trust their partner and wants to know if they’ve been following accounts on the sly, then unfollowing them to avoid being caught. It could, alternatively, be used by an employer who wants to snoop on an employee who might be following and then unfollowing accounts in a search for alternative work.
HOW ‘SOFT HACKING’ A TWITTER ACCOUNT WORKS
Before I get started, let me stress that this doesn’t provide you with some kind of exhaustive list of all the accounts a given user has ever followed. It’s selective, and it’s pretty hit and miss. But in some circumstances, this technique can reveal a lot more about an individual’s Twitter use than they’d want revealed. Here’s how it works…
Set up a brand new Twitter account. It has to be brand new. If you’ve used the account in any way whatsoever before, this won’t work.
Once your account is set up, protect it, then follow the account of the person you want to ‘soft hack’. DON’T do anything else. Don’t follow anyone else, don’t search for anything, and don’t visit anyone else’s page. If you do any of these things whilst you’re logged into that account, you’re diluting the results, and you could lose most of the insight.
Log out, or close the browser, then log back in again. If you want, you can even unfollow the account once you’re logged back in. The association should still remain.
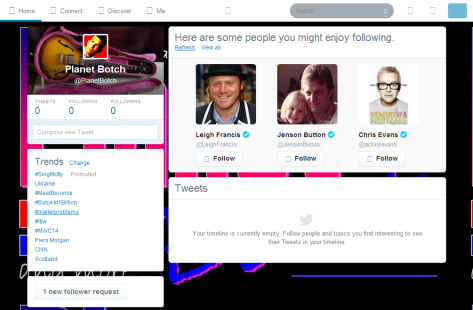
Now look at your follow suggestions. Because your account is new, in the main desktop view the suggestions will come up along the top of the screen above the timeline. If you’ve never followed anyone at all, or used the account in any way, you’ll get a generic selection of suggestions based on trends in your region. Most of the accounts will be ‘blue ticks’ – almost invariably celebrities and verified household names relevant in your part of the world. In the screen grab below, you can see a typical serving: three ‘blue tick’ celebs for Central England…
But once you’ve followed someone, the suggestions change. What you’ll see now, is a mix of household names, and PEOPLE IN WHOM THE PERSON YOU ARE FOLLOWING IS DEEMED, BY TWITTER, TO HAVE AN INTEREST.
Naturally, if you’ve followed lots of people, the privacy implications are minimal, because Twitter could be basing its suggestions on any or all of the accounts you’re following. You can’t pin any suggestion down to one account. But if you’ve only ever followed one account, as is the case here, you know that any suggestions other than the big name generics, must be accounts in which the one person you’ve followed is deemed to have an interest.
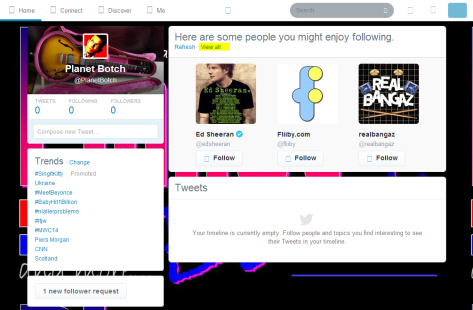
Even if the person you’ve followed has unfollowed those accounts, they can still potentially show as suggestions. Below there’s an example. One obvious ‘blue tick’ celeb, but who are the other two? Never heard of them? Maybe not. But Twitter deems your chosen subject to have an interest in them. They could be accounts he or she is following, but they may also be accounts he or she only temporarily followed, or has been linked with in some other way, and that’s where things get interesting…
Now click the small “View all” link above the timeline (as highlighted yellow in the pic above). What this does is presents you with a list of accounts. For me, at the time of writing, this list comprises a top section which will be made up purely of accounts which Twitter cites as interests of the person you’ve followed, and a bottom section made up mainly or wholly of generic household names. The dividing line is not marked, but it shouldn’t be difficult to work out where it falls. You can now simply browse the accounts in the top section of the list for an insight into the people in whom your chosen subject is deemed to have an interest.
DO I SEE EVERYONE THE PERSON HAS FOLLOWED?
These are only follow suggestions, determined by Twitter’s automated algorithms, so you’ll only see accounts Twitter thinks are significant. If your husband’s been slyly and sporadically following Tamara from work with her 45 followers and general disinterest in social networking, you’re unlikely to see her account come up, because Twitter probably won’t regard a smaller, less active account as greatly important. But if he’s been following dating agencies or escort agencies whilst your back is turned, you could be much more likely to find out about it because those accounts may have high influence, and to Twitter, influence is key.
Trends in the follow suggestions would make a more reliable guide than the odd one, isolated account. If one dating agency shows up, it could, theoretically, be linked through a third party and the user in question may never have actually followed it. If, on the other hand, three dating agencies and two escort agencies show up, that could fairly be considered a trend, and a few questions probably do need to be asked…
Whilst this is not an exact science, the technique does have the potential to reveal information about an account holder, which that individual would not want anyone else to know. It should also be recognised that this is only one way to ‘soft hack’ a social networking account and glean information a given user might be mortified to discover is publicly available. There are others, all of which exploit the inability of these networking sites to keep potentially sensitive information under wraps.
In the end, of course, an employee accused of following a rival company, or a husband accused of following a dating agency, can blame Twitter’s software and insist they never followed those accounts – and I’m sure that’s exactly what they’d do. This is never going to serve as evidence, which is one of the reasons I think ‘soft hacking’ is an appropriate term. But it is, nevertheless, a disrespect of user-privacy on Twitter’s part. Yes, you can say that if someone doesn’t want to be found out for following an account, they shouldn’t follow it in the first place.
But the point is that these systems of linking user information and then presenting it to other, random users, are exceptionally creepy. People DON’T know how easily their protected accounts can be compromised, and many don’t even know they’re being followed invisibly. They SHOULD know. Everyone is entitled to a certain level of privacy, and this, most definitely, is not it.
You must be logged in to post a comment.